Cybersecurity
Cybersecurity Visibility
Your Cybersecurity Strategy Starts Here

Network Visibility for Cybersecurity
Higher ROI – A single investment in Cubro can reduce long-term cybersecurity expenses by cutting licensing, bandwidth, and maintenance costs.
Better Security Outcomes – Security tools perform better when they receive only relevant traffic, improving overall threat detection and response.
More Strategic IT Investments – Instead of overspending on bigger security tool licenses, companies can allocate budgets more effectively.
Enterprise Security
How Network Visibility Empowers Enterprise Security
Since enterprises have started to use the cloud more extensively, the network environments have become more challenging to monitor and protect. Traditional tools often struggle to keep up with this scale and complexity, leading to inconsistent visibility and potential blind spots.
Cybersecurity Monitoring
What is Cybersecurity Monitoring?
Cybersecurity monitoring is the automated process of collecting and analyzing indicators of potential security threats and triaging them with appropriate action.
Security operations teams have an ever-increasing amount of work and responsibility in maintaining the overall health, performance, and security of a business’ infrastructure as technologies evolve, complexity increases, and enterprise networks continue to grow.
Data Breaches
The High Cost of Data Breaches
Today cybersecurity monitoring is part of a company’s compliance and regulatory requirements. Data breaches can be costly in many ways: ransom cost, fines and compensations, bad publicity, lower brand value and paused operations preventing business activities. Some of these can have a long-lasting impact on the company, including lowered stock value.
Network cybersecurity monitoring’s core objective is to minimise downtime by preventing attacks and preserving data to keep an organization operational. By combining attack and passive security monitoring and automating the processes as much as possible, organizations can protect themselves from network threats and identify attackers.
Cybersecurity Pain Points
Common Cybersecurity Pain Points in Large Enterprises
Several tools are on the market for security departments or security operations centres (SOC). SOC is the team and infrastructure responsible for managing an organization’s security posture, leveraging tools like SIEM and SOAR. Security information and event management (SIEM) collects and analyzes security data, identifying potential threats. Security orchestration, automation and response (SOAR) automates and orchestrates responses to security incidents, improving SOC efficiency.
Network detection and response (NDR) refers to a category of network security products that detect abnormal system behaviours by continuously analyzing network traffic. Endpoint Detection and Response (EDR) is used for unusual activity on system endpoints, including computers, phones, and servers.
Together, network and security monitoring provide comprehensive information, analysis, and reports. The aim is to automate these functions as much as possible.
Automation tools and particularly agentic AI help in making these tasks easier.
Finding the Right Balance
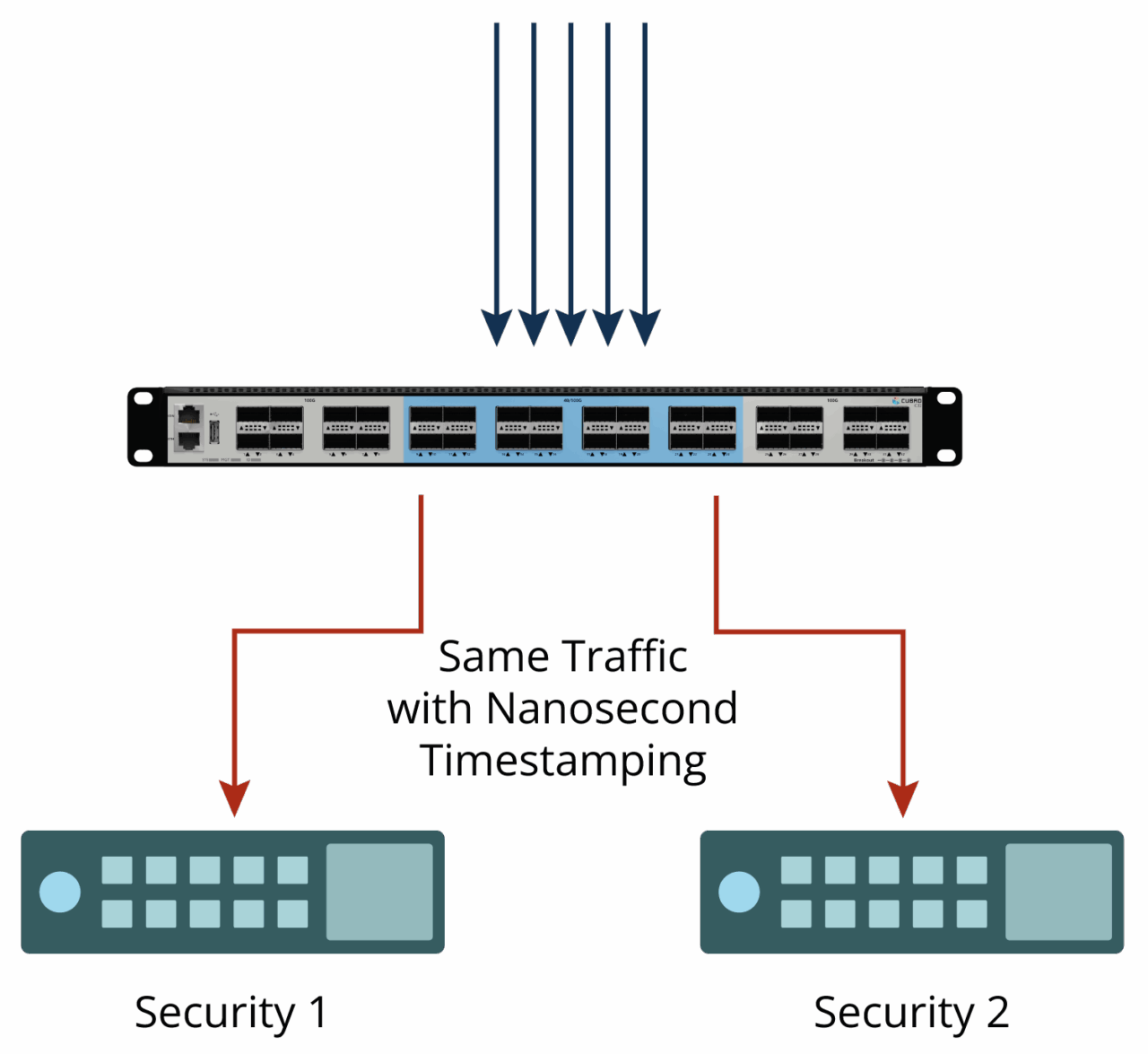
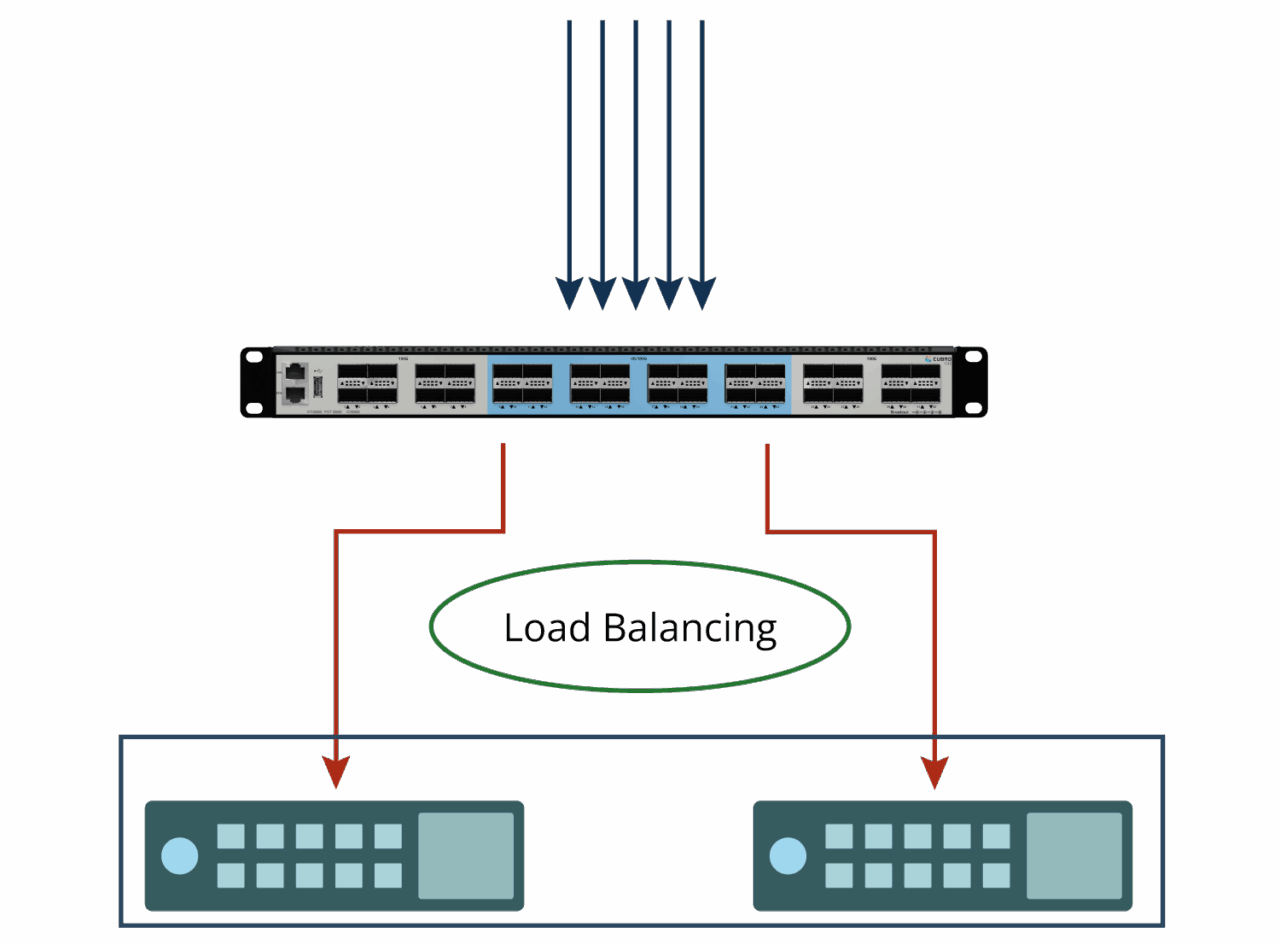
On the one hand, it is tempting to choose the best of breed tools to create a best of industry service operation centre, but integrating
them always comes with a cost. On the other hand, one vendor solution minimises the integration costs, but the risk of vendor lock-in is not appealing. Often, one vendor solution is criticised for its limited agility. Network Packet Brokers increase flexibility by providing the option of sending the same or filtered traffic to several destinations. This enables using tools in parallel, for example, when testing and comparing tools to each other or when having tools for specific purposes.
Regardless of what kind of solution is chosen, cost monitoring is essential. The cost overruns are due to licensing, bandwidth charges, and inefficient use of tools. The number of servers often has an impact on the licensing fees and sometimes upgrading the HW and reducing the number of servers can create substantial savings. Bandwidth and efficient use of the tools can be favorably improved by using TAP and NPB solutions.
Another area where TAP and NPB are helping is traffic reduction and filtering to choose only relevant traffic to remove performance bottlenecks. Security tools may require continuous HW and licence upgrades with increasing traffic.
In either case, it is important to have all necessary data for the tools.
Enhance Cybersecurity
Cybersecurity Objectives
Cubro Network Visibility: Achieving Effective Cybersecurity Objectives with Network TAPs and Packet Brokers
In today’s digital age, cybersecurity is more crucial than ever. Protecting sensitive data and maintaining network integrity are top priorities.
Cubro Network Visibility offers solutions to enhance cybersecurity through advanced technologies. Network TAPs and Packet Brokers are key components in this strategy.

These tools provide comprehensive network monitoring, ensuring effective protection against cyberattacks. They help in identifying threats and optimizing data flow.

Understanding how cybersecurity works is essential for implementing robust security measures. Network visibility plays a vital role in achieving cybersecurity objectives.
We explore how Cubro Network Visibility can help secure cyberspace. Learn about the importance of network TAPs and Packet Brokers in safeguarding your digital environment.
Achieving Cybersecurity Objectives: Best Practices and Industry Standards
Achieving cybersecurity objectives requires a strategic approach rooted in best practices and adherence to industry standards. It’s essential to align these objectives with organizational goals for maximum effectiveness.
Implementing cybersecurity measures involves understanding and applying various guidelines. These ensure that systems and data remain protected against threats. Consistent monitoring and assessment play vital roles in the security framework.
Consider the following best practices for achieving cybersecurity objectives:
Regular audits and vulnerability assessments
Adoption of web security standards
Continuous training and education for staff
Adhering to industry standards provides a baseline for evaluating security measures. This approach not only enhances the effectiveness of cybersecurity strategies but also fortifies protection against evolving cyber threats.
Network Visibility for Cybersecurity
Understanding Network Visibility in Cybersecurity
Network visibility is the cornerstone of effective cybersecurity. It allows for continuous monitoring of data across networks, ensuring comprehensive oversight.
Visibility helps identify malicious activities early, enabling swift responses to potential threats. This proactive approach is crucial for cybersecurity protection.
Achieving network visibility involves using tools like Network TAPs and Packet Brokers. These tools capture and analyze traffic seamlessly, without impacting network performance.
Key benefits of network visibility include:
Enhanced threat detection and response
Improved network performance and tool efficiency
Compliance with cybersecurity standards
Effective visibility aids in understanding how cybersecurity works by providing detailed insights into network activities. It also supports meeting industry standards by ensuring data integrity and confidentiality.
Secure Monitoring
The Role of Network TAPs: Foundation for Secure Monitoring
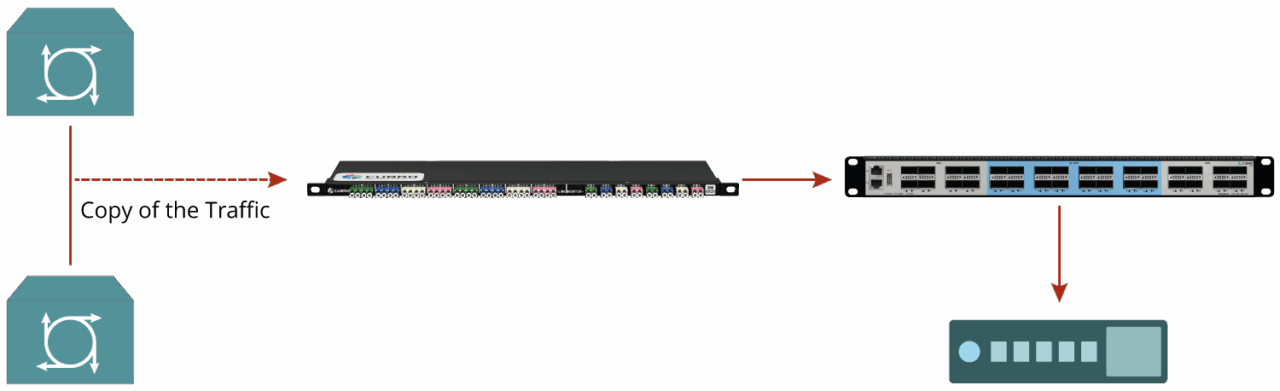
Network TAPs are fundamental to secure network monitoring. They provide a non-intrusive method to capture live data from networks.
Unlike traditional methods, TAPs do not affect network performance. They allow IT teams to analyze traffic without disruption, offering complete data visibility.
Network TAPs offer numerous advantages for cybersecurity, including:
Real-time data capture
High reliability in data monitoring
Prevention of packet loss during analysis
Effective visibility aids in understanding how cybersecurity works by providing detailed insights into network activities. It also supports meeting industry standards by ensuring data integrity and confidentiality.
Data Flow
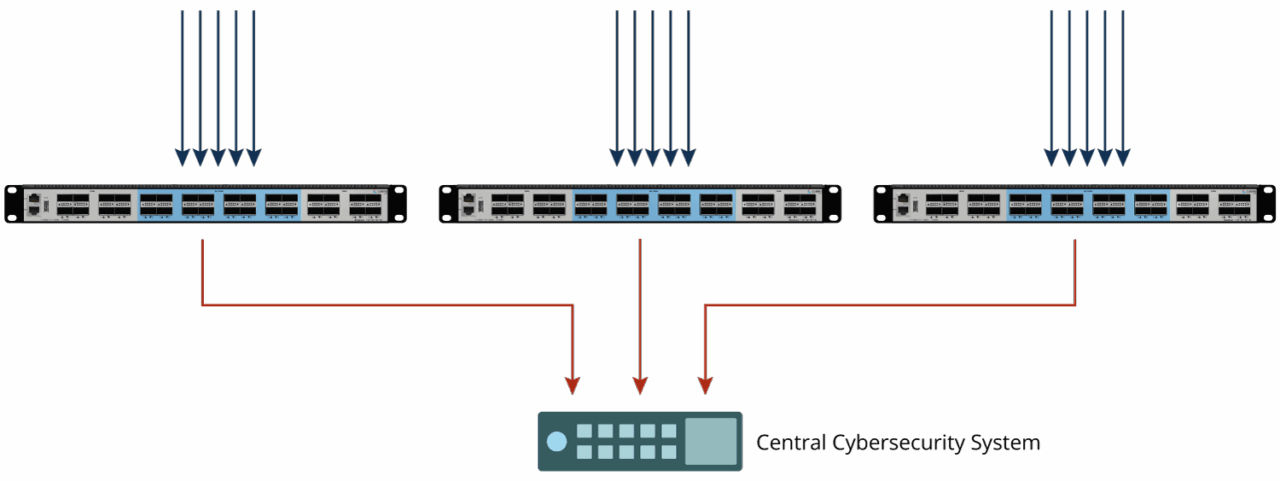
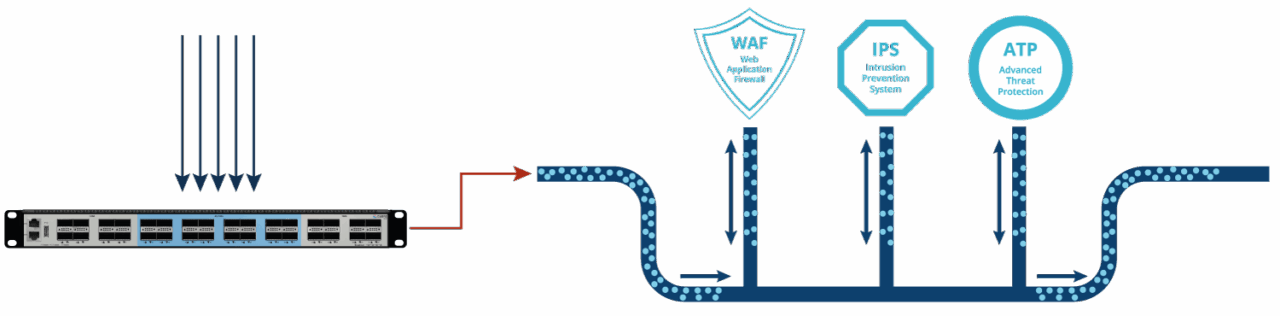
Network Packet Brokers: Optimizing Data Flow and Tool Efficiency
Network Packet Brokers (NPBs) play a crucial role in effective cybersecurity strategies. They manage and direct data from multiple network points to the right monitoring tools.
NPBs perform several critical functions that ensure optimal network performance. They intelligently filter and distribute traffic, enhancing tool efficiency and preventing data overload.
Key benefits of using Network Packet Brokers include:
Traffic aggregation from diverse sources
Load balancing across multiple tools
Advanced filtering and deduplication capabilities
By optimizing data flow, Packet Brokers help maintain robust cybersecurity protection. They allow for precise data analysis, ensuring faster identification and mitigation of security threats.
Incorporating NPBs into your cybersecurity framework aids in achieving comprehensive network visibility. This enables quick response actions, safeguarding your systems from potential cyberattacks.
Cybersecurity Protection
How Cubro Network Visibility Solutions Enhance Cybersecurity Protection
The effectiveness of these solutions lies in their ability to offer a holistic view of network activities. This ensures comprehensive monitoring and enhances the security of cyberspace.
Cubro Network Visibility solutions strengthen cybersecurity defenses by providing deep insights into network traffic. This is crucial for early detection of threats and vulnerabilities.
Some key features of Cubro’s solutions include:
- Passive monitoring with Network TAPs
- Efficient traffic management with Packet Brokers
- Enhanced threat detection capabilities
Cubro’s tools also enable adherence to cybersecurity industry standards. This alignment supports regulatory compliance and bolsters overall cybersecurity objectives.
Moreover, Cubro solutions are designed to adapt to evolving cybersecurity challenges. They offer scalable options to address the growing complexity and volume of network traffic.
Incorporating Cubro’s solutions into your network infrastructure equips you with proactive defense measures. This not only protects against cyberattacks but also ensures continuous security monitoring and data integrity.
Advanced Technologies
VXLAN, GRE Tunneling, and Tool Overload Protection
Advanced technologies play a significant role in enhancing network security and efficiency. VXLAN (Virtual Extensible LAN) is one such technology. It boosts network scalability and flexibility, allowing for efficient data routing across virtual networks.
GRE (Generic Routing Encapsulation) tunneling is another critical technology. It facilitates secure data transmission between networks. This protocol adds an extra layer of security, ensuring data integrity and confidentiality during transit.
Managing data effectively is essential to avoid overwhelming security tools. Tool overload protection ensures monitoring tools remain efficient by distributing workloads evenly. This approach optimizes performance and enhances security capabilities.
- VXLAN for scalable networks
- GRE tunneling for secure data transfer
- Tool overload protection for optimized tool functionality
Information Security Strategy
Implementing Effective Information Security Strategies with Cubro
Implementing robust information security strategies is essential in today’s digital landscape. Cubro’s solutions provide a comprehensive approach to enhancing network visibility and security. They integrate seamlessly with existing systems, ensuring no disruption to network performance.
Effective strategies begin with identifying cybersecurity objectives. They must align with organizational goals. Regular audits and vulnerability assessments are crucial for maintaining security posture. Cubro aids these processes by providing actionable insights through its tools.
By leveraging Cubro’s solutions, organizations can strengthen their defenses and enhance overall security strategies efficiently.
Cybersecurity Framework
Conclusion: Building a Resilient Cybersecurity Framework with Network Visibility
Building a strong cybersecurity framework requires effective network visibility. Cubro provides the tools necessary to meet modern cybersecurity challenges. Comprehensive monitoring through Network TAPs and Packet Brokers strengthens security measures.
By utilizing Cubro’s solutions, organizations can detect threats early and respond promptly. This proactive approach reduces risks significantly and enhances data protection. In today’s threat landscape, relying on robust network visibility is essential. Ensuring cybersecurity resilience requires continuously updating and refining security measures. Leveraging Cubro’s technologies equips organizations to face evolving cyber threats confidently and efficiently.
FAQs
Network visibility is the continuous, comprehensive monitoring of data as it traverses a network. It enables early detection of malicious activity, supports swift response, and provides detailed insights into traffic without degrading performance. Strong visibility also improves tool efficiency, helps maintain data integrity and confidentiality, and supports compliance with cybersecurity standards—making it foundational to achieving cybersecurity objectives.
Network TAPs passively capture live traffic without interfering with production networks, ensuring complete, reliable data collection. They deliver real-time visibility, minimize or prevent packet loss during analysis, and avoid impacting network performance. By managing data flow cleanly, TAPs help prevent monitoring tool overload and give security teams accurate, uninterrupted insight into network activity.
NPBs sit between network data sources and security/monitoring tools, intelligently aggregating, filtering, deduplicating, and load-balancing traffic. This ensures the right data reaches the right tools at the right volume, preventing overload and boosting tool efficiency. By optimizing data flow, NPBs enable faster, more precise threat detection and mitigation while contributing to comprehensive network visibility.
VXLAN extends network scalability and flexibility, enabling efficient routing across virtualized environments. GRE tunneling supports secure data transfer between networks, reinforcing data integrity and confidentiality in transit. Tool overload protection distributes workloads to keep monitoring tools performant and effective. Together, these capabilities improve coverage, resilience, and analysis accuracy within a visibility-driven security architecture.
Effective practices include aligning security objectives with organizational goals, conducting regular audits and vulnerability assessments, adopting web security standards, and continuously training staff. Cubro supports these efforts through passive monitoring with Network TAPs, efficient traffic management via Packet Brokers, and enhanced threat detection, delivering actionable insights, compliance support, and scalable visibility that adapts to evolving threats.

Our newsletter provides thought leadership content about the industry. It is concise and has interesting content to keep you updated with what’s new at Cubro and in the industry. You can unsubscribe anytime with a single click.
Your e-mail address is only used to send you our newsletter and information about the activities of Cubro Network Visibility. You can always use the unsubscribe link included in the newsletter.