Network Visibility for VXLAN Overlay Networks
Getting accurate Visibility in Overlay and Underlay Networks
Attaining total visibility into overlay networks while maintaining logical separation of traffic contained within poses a significant challenge. The use and quantity of network overlays are exploding with the rapid expansion of NFV deployments and VXLAN is often the protocol of choice in a Fabric Spine – Border Leaf architecture. With all the advantages overlays provide they also increase complexity and complicate network visibility as relevant information becomes hidden in VXLAN tunnels. Traditional monitoring tools are often unable to process VXLAN encapsulated information leading to gaps in visibility.
Technical Solutions from Cubro
Cubro´s Advanced Network Packet Brokers are the perfect choice for modern VXLAN networks supporting all required functions to handle VXLAN tunneled information such as
- VXLAN tunnel stripping
- VXLAN outer tunnel filtering like VXLAN VNI tunnel identifier
- VXLAN inner tunnel filtering like inner IP and/or inner TCP/UDP port number
- Simultaneously outer and inner VXLAN tunnel filtering
These superior functions will protect monitoring systems from being overloaded and will ensure that existing monitoring systems can be also used for VXLAN network traffic.
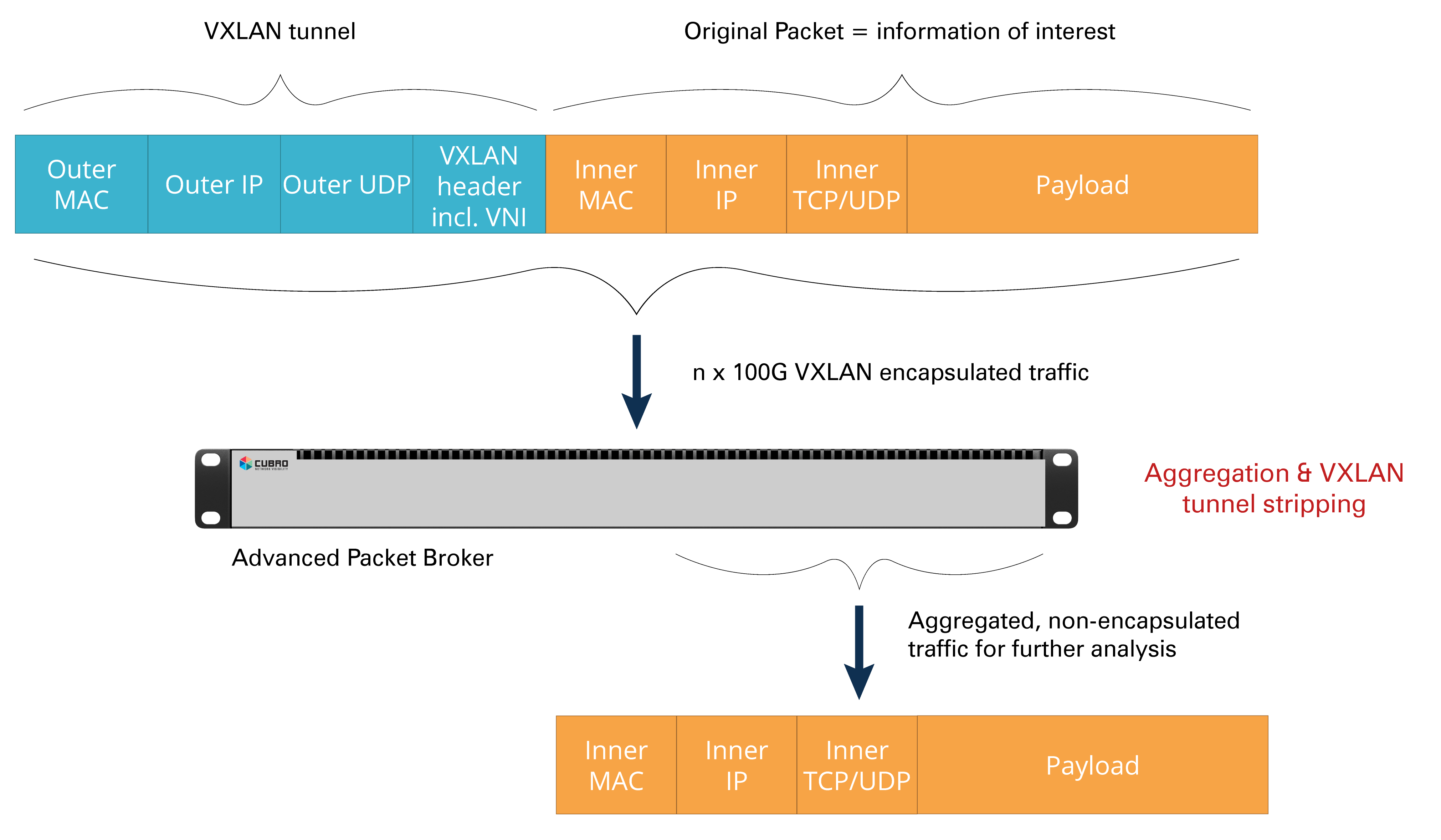
VXLAN tunnel stripping
VXLAN encapsulation adds a 50 Byte tunnel header to the original packet. Not only is packet size increased but the original information also becomes hidden inside the VXLAN tunnel. Monitoring systems require the original packets, however, they are not usually able to process VXLAN tunnel headers. By enabling VXLAN stripping on an Advanced Packet Broker from Cubro the tunnel headers are no longer an issue for the monitoring system as the Packet Broker will automatically look for VXLAN packets and strip the VXLAN tunnel without any further user interaction.
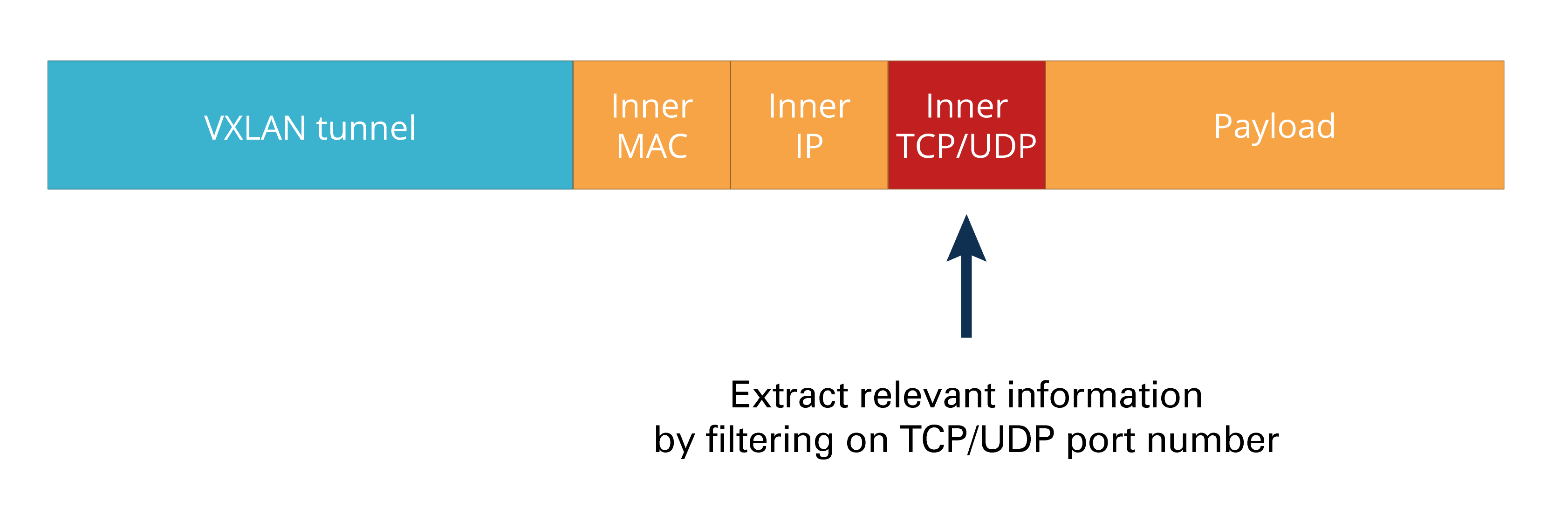
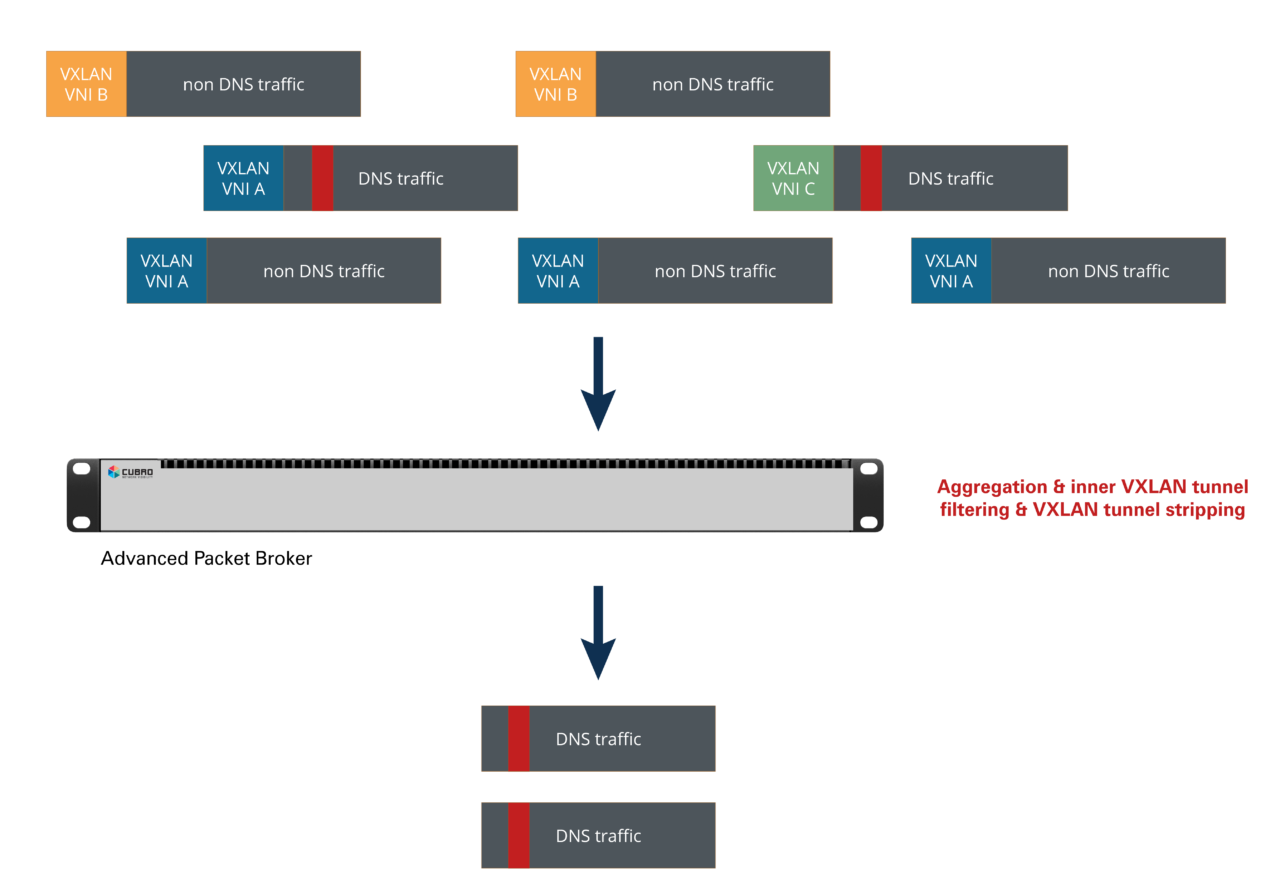
Inner VXLAN tunnel filtering
In order to protect monitoring systems from overload, only relevant traffic should be forwarded to them, therefore, filtering out irrelevant packets from incoming traffic is highly required. However, in any tunneling application the relevant traffic is hidden and filtering inside tunnels is required; filtering with traditional Layer 2 to Layer 4 devices will not be enough because such systems can only interpret the outer header information.
- Remove & correlate flows across the path
- Correlate flows based on the underlay transport information
- Combine flow/path segment based on BGP
- Enrich data from switch inband telemetry
- Enrich data with switch table information
Example:
DNS traffic running with UDP Port 53 inside a single or multiple VXLAN tunnels can be easily identified and filtered allowing that a DNS monitoring system will be protected from being overloaded by having to process non-required (i.e. non DNS) traffic.
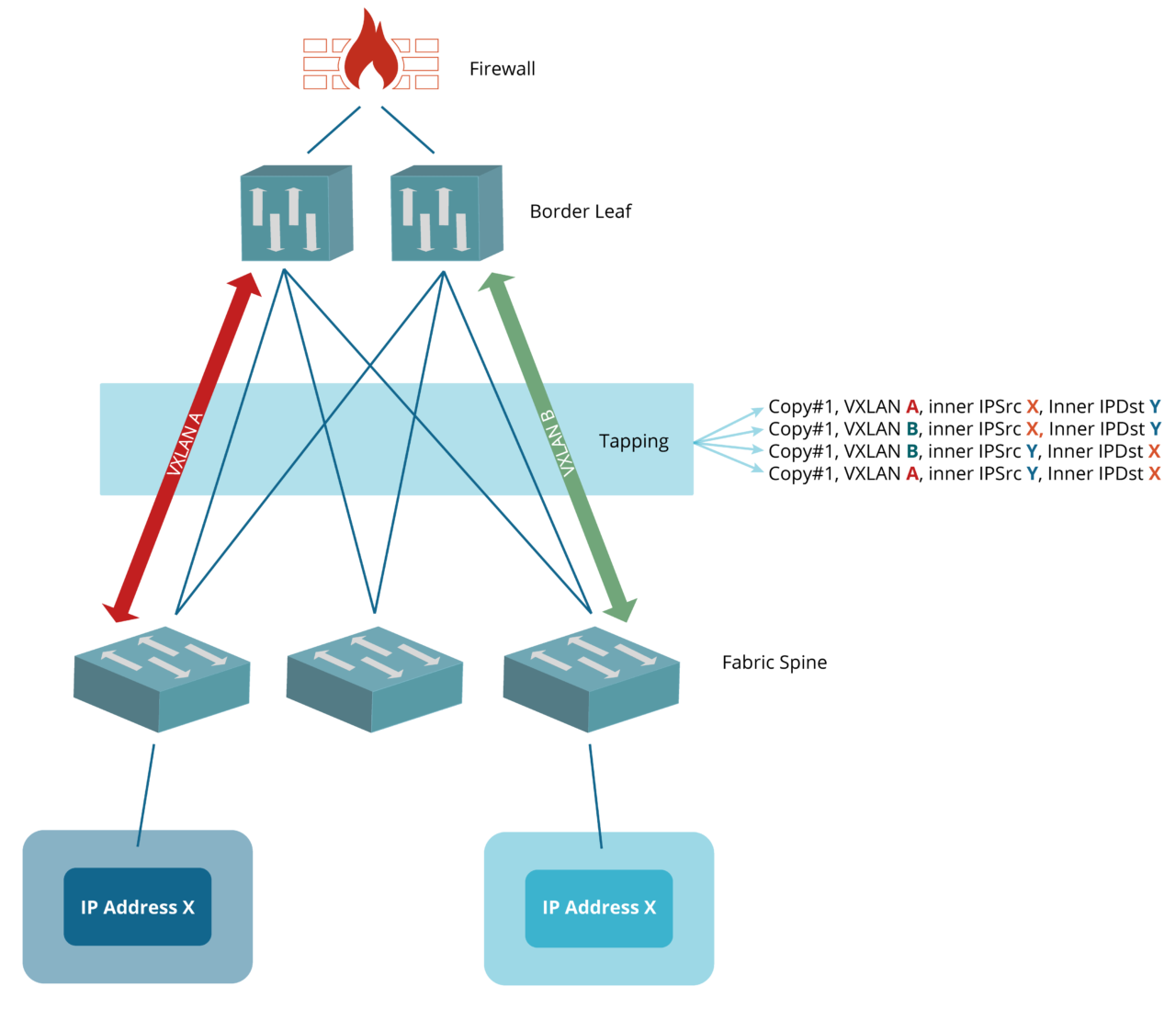
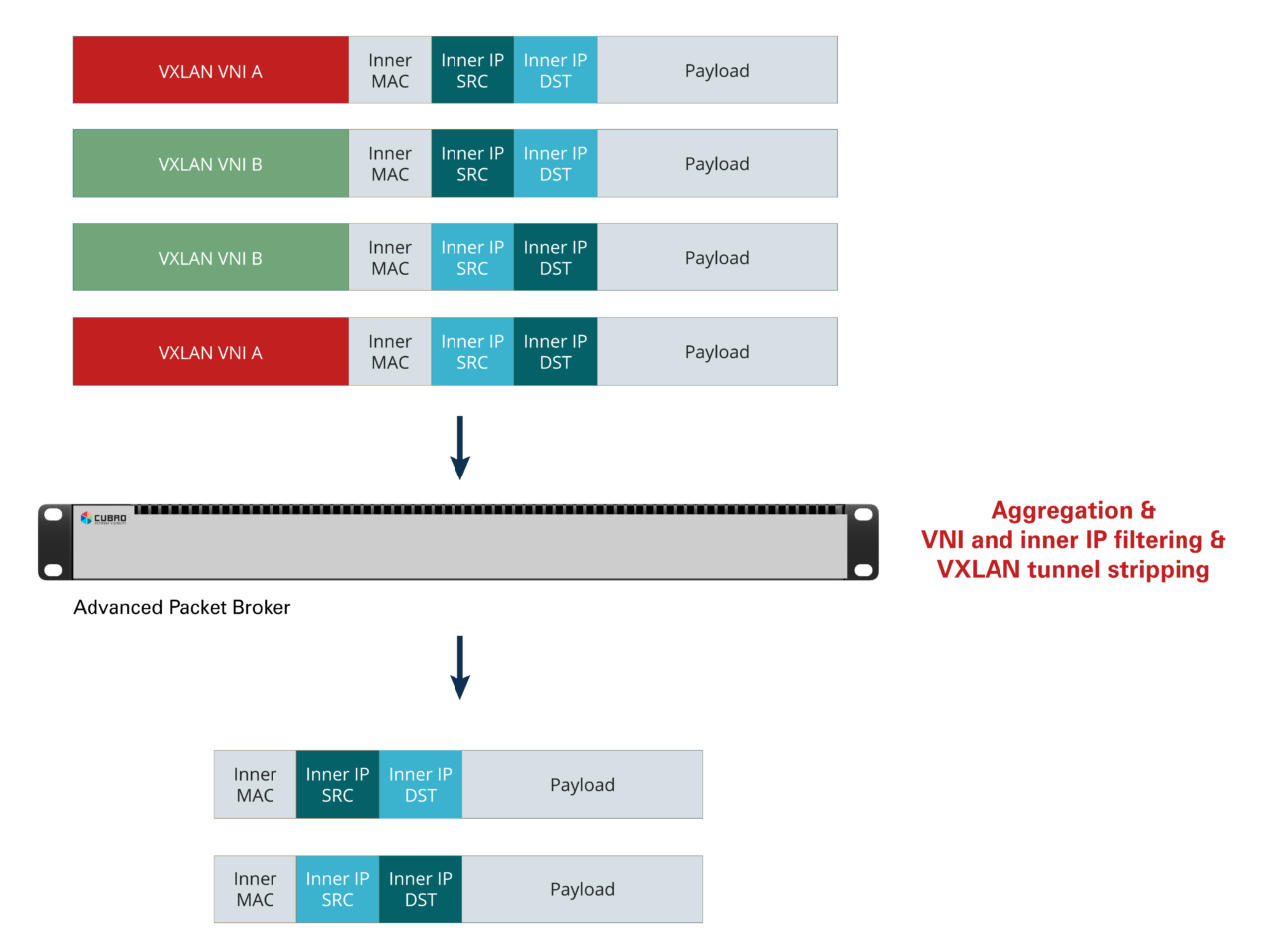
Combining outer and inner VXLAN tunnel filtering
Advanced Packet Brokers from Cubro support filtering in the outer and inner VXLAN tunnel simultaneously. In a typical Fabric Spine – Border Leaf architecture information/packets might become duplicated.
When IP X talks to IP Y the tapped traffic is available in two copies (=duplicated). The only difference between the two copies is the VXLAN VNI. Actually the same packet is available with VXLAN VNI A and also with VXLAN VNI B. By filtering on the VXLAN VNIs and inner IPs, duplicates can be dropped, reducing the load to monitoring systems easily. As this deduplication solution is done in hardware the throughput is in the range of Tbit/s.
VXLAN Head Stripping
Strip VXLAN headers at the Ingress to support legacy monitoring tools
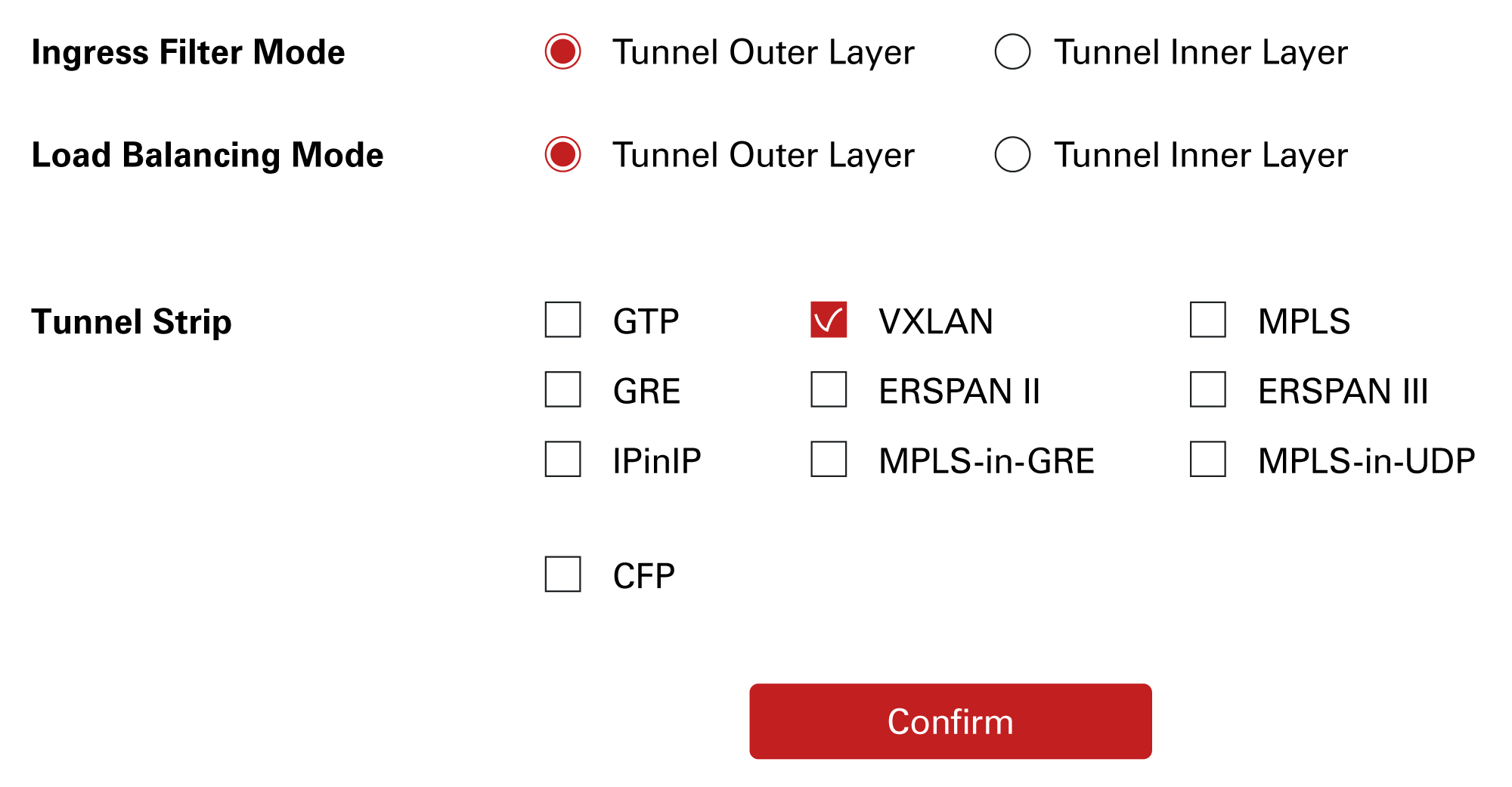
VXLAN Termination must be enabled on the interface where traffic enters the packet broker.
Within the Forwarding Policy configuration, navigate to the Ingress Port Group Settings by clicking on the desired group. Inside the Port Configuration menu, you can select specific tunnel types to be stripped from the traffic. Once your selection is confirmed, the headers are removed automatically—no further configuration is required to decapsulate your traffic.
Products in this Solution

Our newsletter provides thought leadership content about the industry. It is concise and has interesting content to keep you updated with what’s new at Cubro and in the industry. You can unsubscribe anytime with a single click.
Your e-mail address is only used to send you our newsletter and information about the activities of Cubro Network Visibility. You can always use the unsubscribe link included in the newsletter.