Make Networks more secure with DNS Traffic Analysis
Getting Better Visibility to DNS Traffic
DNS is increasingly being recognised by security professionals as a potential threat vector for attacking a network. DNS is prone to any number of notable exploits that have been leveraging its insecure but ubiquitous nature including redirection of DNS queries and cache poisoning (often to malicious sites), network footprinting (via leakage of zone information and reverse queries), denials of service, and even data exfiltration.
DNS information is neither authenticated nor validated (excepting the instances where DNSSEC is employed), so the only way to ensure that DNS is functioning as intended in your organisation is firstly through careful configuration and hardening of your organisation’s DNS servers. Second, is through careful monitoring of the DNS traffic on the network.
Technical Solution from Cubro to Monitor DNS Traffic
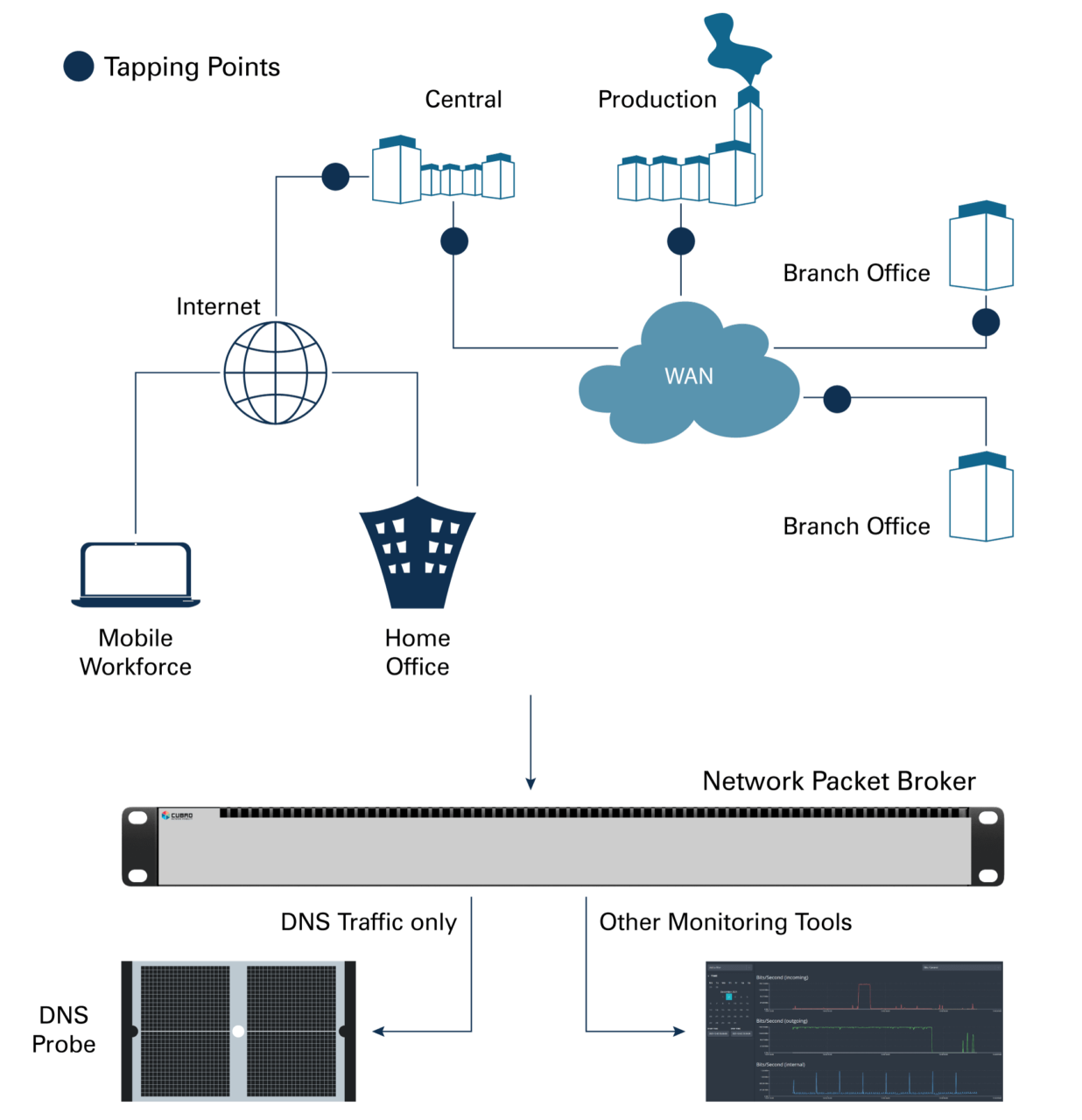
Careful monitoring, in turn, requires complete visibility into your network traffic and this is where Cubro Network Visibility can help. Using our comprehensive lineup of high-quality network TAPs (Test Access Points), an organisation will have unfettered access to all the traffic on its network. Cubro’s Network Packet Brokers can gather this data for aggregation, replication, and filtering of traffic to monitoring systems and security tools; and that includes the ability to isolate and inspect DNS traffic.
The Domain Name System is a complex distributed database on which most Internet services rely. Its monitoring is critical, and it is necessary to continuously monitor DNS traffic to identify anomalies, measure performance, and generate usage statistics.
Such analysis of DNS traffic has a significant application within information security and computer forensics, primarily when identifying insider threats, malware, cyber weapons, and advanced persistent threat (APT) campaigns within computer networks.
While a primary driver for DNS Analytics is security, another motivation is understanding the traffic of a network so that it can be evaluated for improvements or optimization. Leveraging DNS data to detect new Internet threats has been gaining in popularity in the past few years.
DNS has a huge impact on overall network performance. It is the Achille’s heel of the web. It is often forgotten, and its impact on performance ignored until it breaks down. The typical problems related to this are:
- Low-Performance DNS Server
- Too many requests
- Delayed answers
- Low time to live in DNS Cache
DNS traffic runs on UDP (or TCP) Port 53 and can be extracted by filtering on Port 53.
All Cubro Packetmasters allow filtering up to OSI Layer 4; all Cubro Sessionmasters allow filtering up to Layer 4 AND beyond! The devices only forward the required traffic to analysis tools and do not overload analysis tools.
Cubro Packetmaster and Sessionmaster products are the perfect choices to get access to DNS traffic – regardless of whether traffic is IPv4, IPv6, or encapsulated within VXLAN, GRE or GTP tunnels.
Products in this Solution

Our newsletter provides thought leadership content about the industry. It is concise and has interesting content to keep you updated with what’s new at Cubro and in the industry. You can unsubscribe anytime with a single click.
Your e-mail address is only used to send you our newsletter and information about the activities of Cubro Network Visibility. You can always use the unsubscribe link included in the newsletter.