Strategies for protecting enterprise IT assets have changed dramatically in the last few years. Bring-your-own-device (BYOD), Work-from-Home (WFH), Internet of Things (IoT), along with increased use of Software-as-a-Service (SaaS) and multi-cloud computing, mean that the enterprise perimeter has disappeared. A new threat landscape has emerged, and enterprises should simply assume that bad actors may already have access to their networks and data.
To respond to this, a new approach to network security is also being developed: the Zero Trust Network Architecture. Some key principles of Zero Trust include:
- Verification
- Verify and authenticate on an ongoing basis
- Give minimal access
- Segment the network to create small zones of control
- Control access to applications, data, and resources
- Grant least privileged access based on need or role
- Assume a breach and continually assess risk
- Plan as if attackers are both inside and outside the network
- Forget the concept of a “trusted zone” (e.g., in the office)
Cubro Visibility products, together with Cubro security solution partners, can play a critical role in protecting enterprise computing access by continually monitoring network activity on the network to identify and remediate these new threats. Cubro is also exploring the latest in machine learning, and artificial intelligence, together with up-to-the-minute threat intelligence which can offer proactive monitoring.
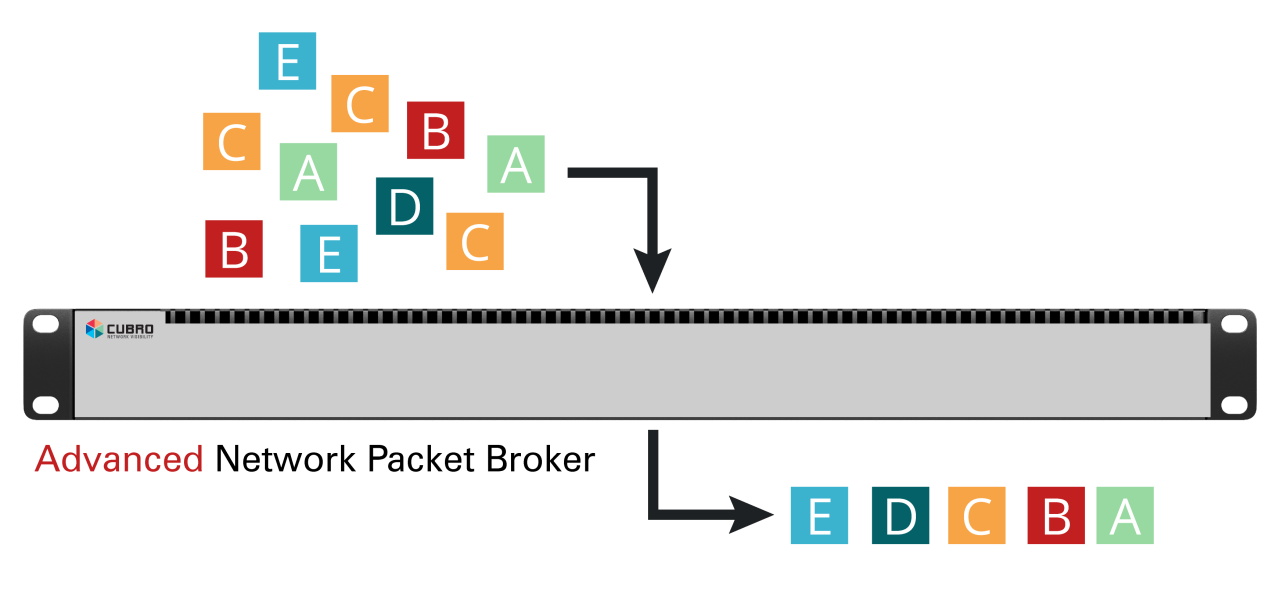
Visibility starts with Cubro’s fully passive network TAPs. Network TAPs provide fail-safe access to all network traffic by providing an out-of-band copy of everything that crosses the wire, ensuring nothing is overlooked. The copied traffic is then fed from the TAPs to Cubro’s Network Packet Brokers to groom the network traffic to meet the needs of security tools. Traffic filtering, de-encapsulation of tunneled traffic, deduplication, and session-aware load-balancing are just some of the services Cubro packet brokers provide to security solutions. Cubro Packet brokers can also generate network flow meta-data in the form of industry-standard Netflow or IPFIX that some network security tools may prefer to ingest.
Two security tools that are especially helpful in implementing Zero Trust Network Architecture include Security Information and Event Management (SIEMs) systems, and Network Detection and Response (NDR) systems. These tools continually monitor either network packets or network flow metadata for intrusions and threats. Cubro Visibility provides packet and flow data for a variety of Industry-leading monitoring platforms.
Contact Cubro via email at support@cubro.com to learn more about Cubro Network Visibility support for security solutions and Zero Trust Network Architectures.